New Data Insights Report Reveals Key Supply Chain Cyber Security Weaknesses
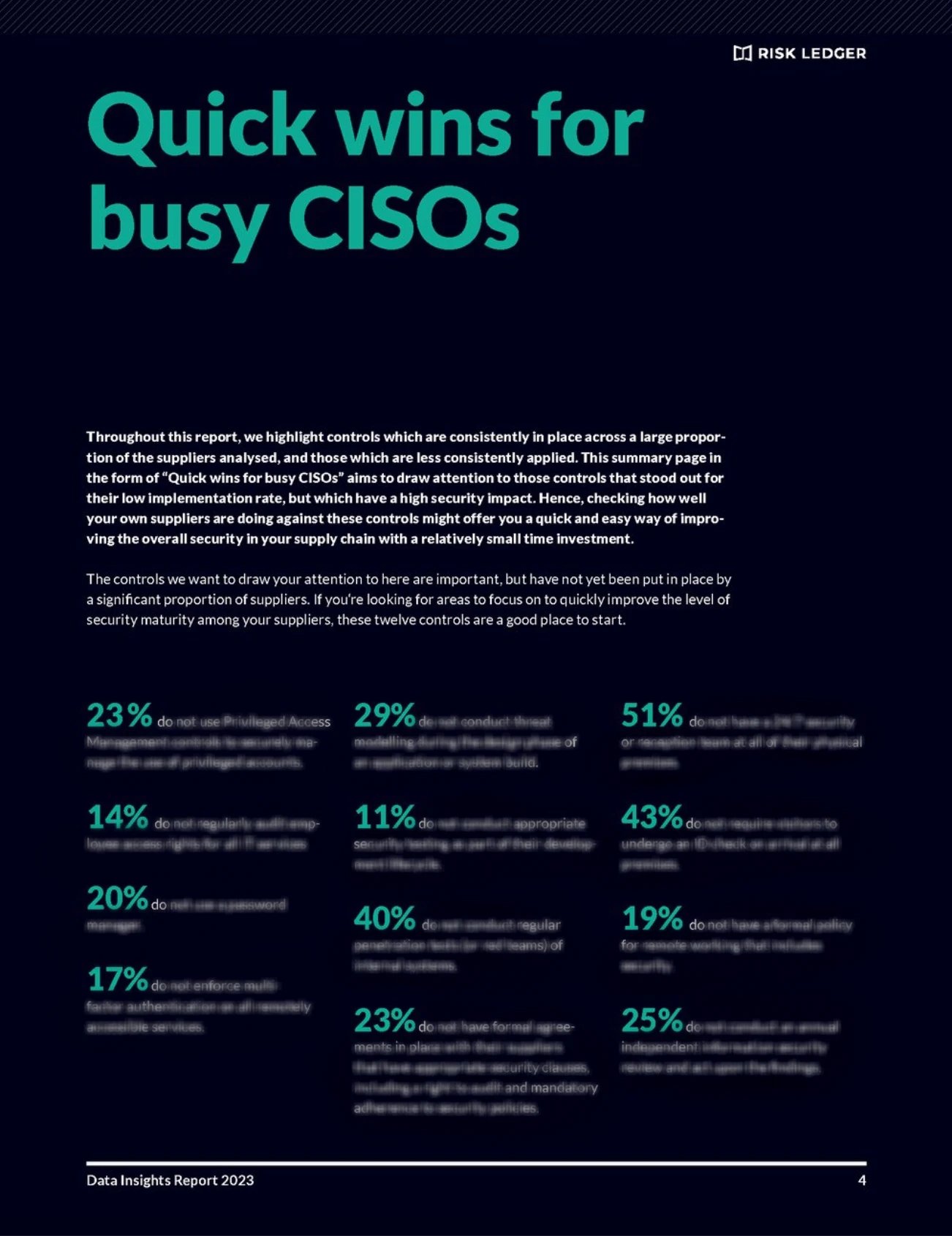
We analysed the security postures of 2500+ suppliers against 200 risk controls and found that 40% of third-party suppliers do not conduct regular penetration tests of internal systems and 20% do not use password managers, putting their own and their customer’s data at risk. This is just a small snapshot of what we found. How are your suppliers doing against these and other controls?
Use our findings to benchmark your own suppliers against the latest security trends, discover potential blind spots, and work in partnership with your suppliers to keep your company secure and make us all safer.
Download your free report today.
Benchmark Data
Our report provides you with data on suppliers' performance against risk controls in the following six cyber security domains that you can use to benchmark your own suppliers:
- IT Operations
- Software Development
- Network & Cloud Security
- Supply Chain Security
- HR & Physical Security
- Security Governance
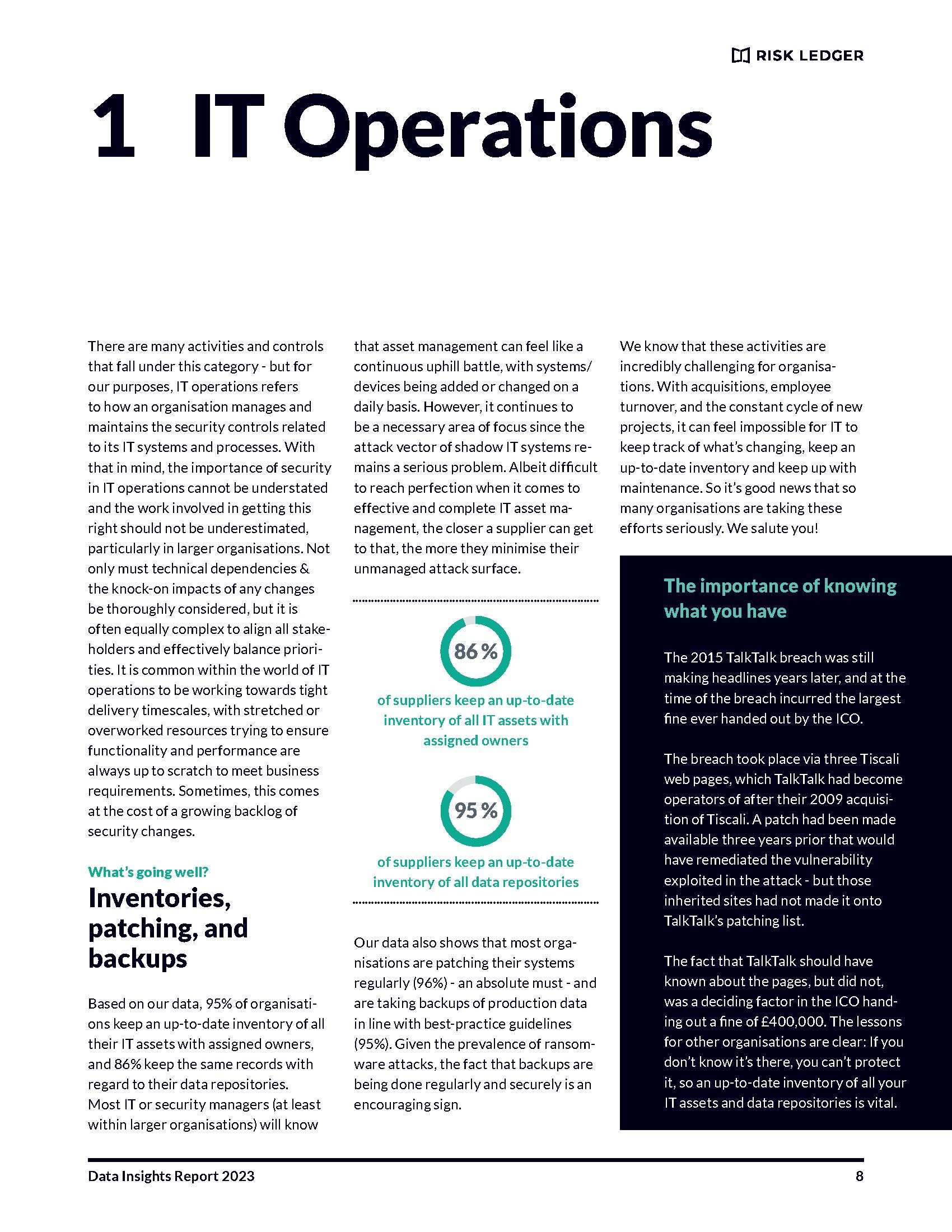
Quick Wins for Busy CISOs
Cognisant of the fact that busy CISOs and other security professionals are constantly evaluating how to spend their limited time most effectively, we have compiled a list of 12 controls that stood out for their low implementation rate, but which have a high security impact. Hence, checking how well your own suppliers are doing against these controls might offer you a quick and easy way of improving the overall security in your supply chain.

Practical Recommendations
The report also provides you with a set of practical recommendations for how to gain cyber security benefits through enhanced supplier engagement.
For instance: Ask your suppliers what methods they use to ensure they stay on top of asset management as and when things change across their organisation. This will give you an idea of how well thought-out these processes are and give you some confidence over how likely it is that they miss something important.
"Companies rarely run security assurance against more than 10% of their immediate third-party suppliers, while the risks from incidents further down the supply chain, in 4th and 5th parties, remain under-appreciated. To improve security in the supply chain, the first step is to gain better data and insights into prevailing weaknesses, and to then focus efforts on these areas and on collaboratively resolving them together with your suppliers. Our new report on The State of Cyber Security in the Supply Chain offers this benchmarking data."
-Haydn Brooks
CEO of Risk Ledger
Supply chain cyber attacks increased by over 600% in 2022 alone...
Attackers are increasingly targeting under-resourced suppliers with weaker defences as a way of disrupting or compromising larger organisations.
Given the staggering increase in supply chain attacks, and their apparent success, it is clear that traditional approaches to third-party risk management have failed. They are often mere paper shields, but also focus only on individual suppliers and not on risks in the wider supply chain. In times of increasing geopolitical tensions, with malign state actors in particular stepping up their attacks on our industries through third party supplier networks, there is now an urgent need to act and do better to ensure business continuity.
What is needed first and foremost is better data in order to identify the leading risks in the wider supply chain ecosystem, and to then tackle these risks as a necessary first step.
It is for this purpose that Risk Ledger has published its new report: "The State of Cyber Security in the Supply Chain: Data Insights 2023" and is making its data-driven insights and recommendations available to the wider security community.
2500 suppliers have shared data on their security posture against more than 200 security controls across 6 key cyber security domains on the Risk Ledger platform, providing us with valuable insights into existing strengths, but also prevailing risks and shortcomings in the supply chain.
We hope that our data, and the insights and recommendations based on it, will help you make informed decisions on where to invest your limited time and resources to improve your overall supply chain security.
Our Methodology:
The data presented within this report is based on an anonymised aggregation of information provided by 2525 of the suppliers using the Risk Ledger platform to showcase their security controls to their clients and customers. When a supplier joins Risk Ledger, they complete a security profile consisting of 211 control questions spread across twelve risk and security domains. The full Risk Ledger framework, with the exact questions and guidance provided to suppliers, can be found here.
This report focuses only on the cyber security aspects. We will look to publish future reports that will also cover Business Resilience, Data Protection, Financial Risk and ESG.
The geographical representation is as follows (among the 6% ‘Other’, there are an additional 47 countries represented):
United Kingdom (62%), United States (20%), Australia (3%), Canada (2%), Germany (1%), Ireland (1%), Sweden (1%), Israel (1%), France (1%), Netherlands (1%), India (1%), Switzerland (1%), Other(6%).
Not every supplier has answered every control question. When a supplier completes their profile on Risk Ledger, the framework dynamically adjusts the questions being asked depending on foregoing answers provided, removing questions which are not relevant for them. So, for example, if the supplier does not develop any applications or systems that collect, process, or store data on behalf of clients, they will not have to answer the control questions within the Software Development domain. For each control presented in this report, the data only relates to suppliers for which the control question was relevant.
Not all controls are included in this report. This report focussed on key control areas known to be most interesting and beneficial to the readers.
The data was pulled from our platform in late March 2023.